As technology continues to advance, so does the landscape of cybersecurity. One of the most exciting and potentially disruptive developments in this field is quantum computing. Quantum computers have the potential to revolutionize many aspects of cybersecurity, from encryption and decryption to threat detection and cryptography. In this blog post, we will explore the impact of quantum computing on cybersecurity and the challenges and opportunities it presents.
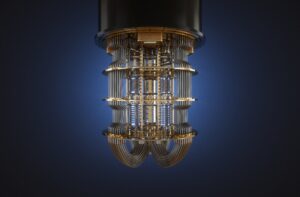
Understanding Quantum Computing
Before delving into its applications in cybersecurity, let’s briefly understand what quantum computing is. Traditional computers use bits to process information as either 0s or 1s, but quantum computers use quantum bits or qubits. Qubits can exist in multiple states simultaneously due to the principles of quantum mechanics, allowing quantum computers to perform complex calculations at speeds unimaginable by classical computers.
The Quantum Threat to Encryption
One of the most significant concerns surrounding quantum computing and cybersecurity is its potential to break widely used encryption algorithms. Many current encryption methods, such as RSA and ECC, rely on the difficulty of factoring large numbers or solving discrete logarithm problems, which are computationally expensive for classical computers. However, quantum computers, specifically Shor’s algorithm, have the potential to solve these problems exponentially faster, rendering existing encryption methods obsolete.
Post-Quantum Cryptography
To address the looming threat of quantum computing to encryption, the field of post-quantum cryptography has emerged. Researchers are actively developing cryptographic algorithms that are believed to be secure against quantum attacks. These new algorithms aim to provide a secure transition for digital communication as quantum computing matures. Organizations should start preparing for the transition to post-quantum cryptography to protect their sensitive data in the quantum era.
Quantum Key Distribution (QKD)
Quantum computing is not only a threat but also a potential solution to cybersecurity challenges. Quantum Key Distribution (QKD) is a technology that leverages the principles of quantum mechanics to provide secure communication channels. QKD uses the properties of qubits to generate and exchange encryption keys in a way that is theoretically immune to eavesdropping, even by quantum computers. While QKD is still in its early stages of development, it holds promise for securing communication in a quantum world.

Quantum-Safe Cybersecurity Practices
To prepare for the era of quantum computing, organizations should adopt quantum-safe cybersecurity practices. This includes:
- Assessing Vulnerabilities: Identify systems and data that are vulnerable to quantum attacks and prioritize their protection.
- Implementing Post-Quantum Cryptography: Begin transitioning to post-quantum cryptographic algorithms as they become standardized.
- Exploring Quantum-Safe Technologies: Keep an eye on developments in QKD and other quantum-safe technologies for secure communication.
- Enhancing Key Management: Strengthen key management practices to ensure that encryption keys remain secure in a quantum threat environment.
Quantum computing has the potential to reshape the field of cybersecurity, both as a threat and as a solution. While quantum computers pose a significant challenge to existing encryption methods, ongoing research in post-quantum cryptography and quantum-safe technologies offers hope for maintaining data security in the quantum era. Organizations must stay informed about these developments and take proactive steps to secure their digital assets against emerging quantum threats. Quantum computing may be on the horizon, but with careful preparation, we can navigate this new frontier of cybersecurity.


