As technology development accelerates and cybersecurity attack surfaces continue to expand, it’s no mystery as to why cybersecurity is projected to become a $300 billion market by 2024. Businesses have seen the frequency of cyber attacks increase over the years and understand that proactivity is the best practice.
Yahoo knows this as well as anyone, after being embattled in their own years-long cybersecurity catastrophe.
Let’s look at a couple of the biggest security attacks in history; what happened, how they happened, and what we can continue to learn from them.
What Happened?
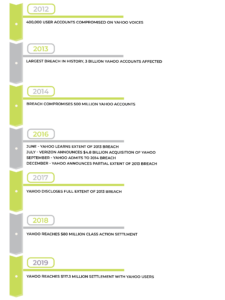
In 2012, an incident took place as a result of an acquisition made with a company who already had lackluster security in place, which ultimately wasn’t updated by Yahoo. Possessing the email addresses and encrypted passwords for hundreds of thousands of users, the hackers published a cache of everything they had online. In some ways, this is a prologue to a years-long cybersecurity disaster that was about to follow, especially when the attackers themselves said at the time that it should be a “wakeup call”.
Throughout the first quarter of 2013 many Yahoo Mail users reported their accounts being hacked, which was achieved by phishing attacks . Users were encouraged by malicious actors to click through links that hijacked their accounts. The hack went largely under the radar at the time, and Yahoo wouldn’t uncover the full extent of the attack for several years.
In 2014, just as the company was discovering that 1 billion accounts had been affected the year prior, hackers were already onto their next venture. Spear-phishing campaigns, which are socially engineered to more specifically target certain groups or individuals, were conducted against Yahoo employees. Successful in their efforts, the hackers installed a backdoor to Yahoo servers, where a copy of the user database was downloaded. The dominoes continued to fall as accounts of interest were identified and cookies were forged in order to access them without a password.
Three separate large-scale attacks occurred from 2012-2014. Although Yahoo had yet to discover that 3 billion, rather than their first estimated 1 billion, accounts had been affected in 2013, their knowledge of the 2014 attack was more complete. Their reports indicated that approximately 500 million accounts were compromised in total. Valuable information was taken including names, e-mail addresses, telephone numbers, encrypted or unencrypted security questions and answers, dates of birth, and encrypted passwords.
Yahoo’s Reaction
Their situation becomes markedly worse over the years as Yahoo’s opaque communication on the matter gets them into serious business and legal turmoil. Following the 2014 breach, the company’s senior teams received internal reports indicating users’ information was being sold on the dark web throughout 2015 into 2016.
As this is happening, Yahoo engages in talks with Verizon about the prospect of acquisition. Throughout negotiations, Yahoo misrepresented their track record of breaches, and failed to disclose what they had recently discovered and were currently investigating.
Just a month before Verizon announces a staggering $4.8 billion acquisition, internal investigations discover the full extent of the 2013 breach. Despite this revelation, Yahoo filed their purchase agreement which intentionally misrepresented their position, affirming the lack of security concerns present in their company.
It took the better part of a year and a half before Verizon and the public were informed of both attacks that took place in 2013 and 2014.
Financial Effects
The ordeal Yahoo found themselves in eventually caught up to them.
For starters, the day following their public disclosure of the 2014 attack, stock prices dropped 3% and $1.3 billion was lost in market capitalization. Realizing they’d been severely misled, Verizon declared a “material adverse event” under the Stock Purchase Agreement. Thus, the two companies came to a new agreement that stipulated a $350 million, or 7.25%, reduction in the price of the acquisition.
Additionally, Yahoo would share liabilities and expenses relating to the breaches. Considering that they did not possess cybersecurity liability insurance, this meant that Yahoo was on the hook for a pretty penny. Aside from expenses spent on forensics and lawyers that totaled $16 million, Yahoo was fined $35 million for failing to disclose, and reached a class action settlement of $80 million in 2018.
Yahoo became the first public company to be fined such an amount by the Securities and Exchange Commission, and the first to make a class action settlement having to do with cybersecurity.
When it comes to 3 billion accounts, Yahoo wasn’t the only one affected, but their entire user base as well. To one extent or another, more than 1 billion people’s information was potentially and definitively being sold on the dark web. As a result, Yahoo agreed to another $117.5 million settlement.
Layer Your Security
Much of what initially compromised Yahoo’s systems was phishing scams aimed at users and employees alike. Particularly when it comes to members within an organization, it only takes one person to click through a maliciously linked email for hackers to potentially gain access to sensitive information. This is why a multi-layered approach to cybersecurity is crucial to businesses these days.
To reduce the risk of phishing attacks, a first layer could be to implement anti-spoofing controls, like spam filters, making it more difficult for hackers to reach users in the first place.
Given that cyber-attacks continue to become more sophisticated and socially engineered, there is still the potential for dangerous emails to bypass the first line of defense. When a user comes across one of these emails, relevant training can be an important layer to help users identify them for what they are.
Unfortunately, these types of attacks are so ubiquitous that no amount of training guarantees users will spot every one of these emails. Preparing for this is another valuable piece to the state of your security. Implementing measures like two-step authentication and proxy servers are but a few ways to protect your organization from undetected phishing attacks.
Lastly, if an incident does occur, responding quickly is crucial. Preparing for such an event means defining a thorough incident-response plan for different scenarios that include legal and regulatory responsibilities.
It is possible that this was the most costly layer that Yahoo seemed to neglect. If they had responded appropriately with the information they had, the reputational and financial ramifications they experienced could have been dramatically reduced.
Stay Safe
There’s a common adage among the cybersecurity community, saying that there are two kinds of companies: those that have been hacked and those that don’t yet realize they’ve been hacked. Everybody has the potential of falling victim to cybercrime, especially as attack surfaces continue to expand.
An end-to-end, multi-layered approach proves to be the best way to mitigate the risk of an attack.
If you want to get ahead and stay ahead of incoming cyber threats, contact us and we’ll map out your cybersecurity future together.


